Fortinet FortiDeceptor - Deception Platform
FortiDeceptor provides early detection and isolation of sophisticated human and automated attacks by deceiving attackers into revealing themselves

FortiDeceptor Hardware Appliances
FortiDeceptor Virtual Machines
Overview
FortiDeceptor, part of Fortinet SecOps Platform, detects and responds to in-network attacks such as stolen credential usage, lateral movement, man-in-the-middle, and ransomware. Adding FortiDeceptor as part of your cybersecurity strategy helps shift your defenses from reactive to proactive with intrusion-based detection layered with contextual intelligence.
Early, accurate attack detection (no false positives) reduces attacker’s dwell time
FortiDeceptor lures attackers into revealing themselves early at the reconnaissance stage by engaging with a wide range of deception assets distributed throughout your environment. The platform generates high-fidelity alerts based on real-time engagement with attackers and malware, providing attack activity analysis and attack isolation. This helps alleviate the burden on SOC teams inundated with false-positive alerts. FortiDeceptor also correlates incident and campaign activities and collects IOCs and TTPs, allowing SOC teams to make smarter, faster decisions.
Watch the VideoAutomatically contains in-network attacks before they spread
When an attacker engages with deception assets, for example, fake files on an endpoint, or if malware tries to encrypt fake file, FortiDeceptor can neutralize the attack by automatically isolating any compromised endpoint. This prevents the attack from spreading and stops communication with a C&C server. This can be done using FortiDeceptor’s built-in, automated attack quarantine capabilities or by sending an alert to SIEM/SOAR for an orchestrated response.
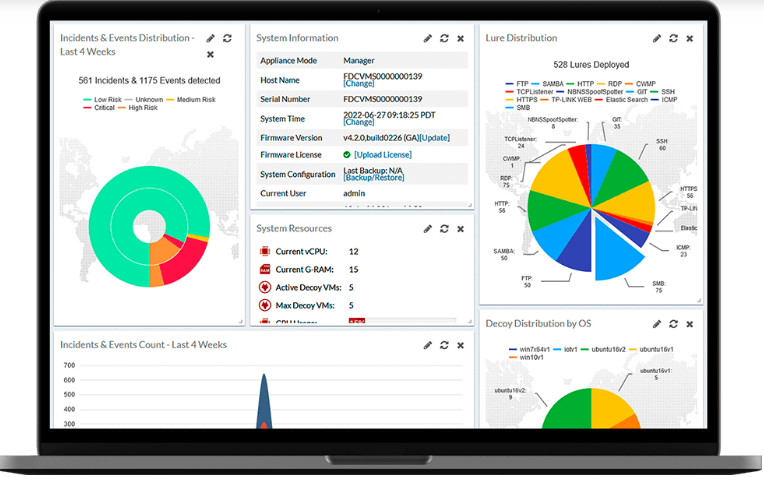
Dynamic protection scales up as the threat level increases
To combat emerging threats and vulnerabilities, FortiDeceptor enables on-demand creation of deception decoys based on newly discovered vulnerabilities, or suspicious activity, providing automated, dynamic protection across OT/IoT/IT environments. Further, FortiDeceptor response capabilities go beyond SOAR evidence enrichment and automated host quarantine playbooks, by providing a SOAR playbook for on-demand deployment of deception assets in response to suspicious activity in your network.
Features and Benefits
![]()
VISIBILITY & ACCELERATED RESPONSE
Integrates with Fortinet Security Fabric and third-party security controls (SIEM, SOAR, EDR, sandbox)
![]()
INSIDER THREAT DETECTION
Reduces dwell time and false positives, detects early recon & lateral movement to misdirect attacks
![]()
FORENSICS & THREAT INTELLIGENCE
Captures and analyzes attack activities in real time, provides detailed forensics, collects IOCs & TTPs
![]()
QUARANTINED/UNQUARANTINED ATTACKS
Infected endpoints can be quarantined away from the production network
![]()
OPTIMIZED FOR OT/IOT/IOMT
Operates in online/air-gapped (offline) modes and a ruggedized version is available
![]()
EASY DEPLOYMENT & MAINTENANCE
Asset-match decoys are automatically deployed with no impact on stability and performance
Use Cases
FortiNDR Cloud and FortiNDR leverage AI/ML, behavioral, and human analysis to analyze network traffic, including encrypted traffic, to detect malicious behavior while reducing false positives.
- DYNAMIC DECEPTION - Network visibility and breach detection via passive footprint. Detects threats to assets that cannot provide their own telemetry.
- RANSOMWARE MITIGATION - Early detection and response to ransomware attacks. Misleads malware to encrypt fake files, triggering automatic blocking of the infected endpoint.
- LATERAL MOVEMENT DETECTION - Detects attackers early in the discovery phase and misdirects lateral activities to the decoy and away from real assets.
- THREAT HUNTING - Enables in-network threat detection, tracks attack origin, gathers TTPs by observing attackers, provides intelligence for rapid response.
- SECURITY FOR IT/OT/IOT/IOMT - Extensive decoys including SCADA systems, IoT sensors are available, plus the ability to upload your own decoys.




